
Identity-based security incidents now affect exactly half of all organizations. From my experience, the correlation is undeniable. Immature programs that rely on manual processes see a higher incident rate than those with mature governance.
Compromised credentials and misconfigurations drive these breaches, costing unprepared companies millions. However, those prioritizing access recertification best practices save up to $1.9 million per incident compared to manual-heavy organizations.
This article explores why most access reviews remain mere theater – and how to turn them into a functional defense.
If your access reviews feel like a checkbox exercise, focus on these core practices:
The rest of this article explains why these matter and how to implement them.
Many organizations treat access reviews like a high-stakes performance – plenty of movement and a lot of noise, but very little substance. Despite the clear risks of over-privileged accounts, the reality is that identity governance often lacks the maturity needed to be effective. Identity-related incidents now cost organizations millions. This is where weak IAM practices translate directly into financial impact.
A startling gap exists between the necessity of robust Identity and Access Management (IAM) and its actual implementation. According to a
2024 Ponemon Institute study, only 45% of organizations have an established IAM program or strategy. This absence of a formal framework means access management is frequently shuffled off to general IT staff who lack specialized expertise.
This "jack-of-all-trades" approach is further crippled by a talent shortage;
roughly 52% of organizations cite a lack of in-house specialists as a primary barrier to securing identities.
The most damning evidence that access reviews are often mere theater is the number of companies skipping them entirely. The same
Ponemon research reveals that 26% of respondents perform no periodic access reviews or certifications whatsoever. When reviews do happen, the methods are often archaic:
Continuing to rely on manual labor in 2026 is a choice to remain vulnerable. The
2025 State of IGA Survey Report highlights that 84% of organizations still lean heavily on manual processes, while a mere 6% have achieved full automation. This inefficiency has a literal cost. Manual reviews require an average of 149 person-days, compared to just 55 days when
user access review automation is implemented.
This is exactly where user access review automation stops being optional and becomes necessary.
Manual access reviews no longer scale with the complexity of modern environments. As an organization grows, the number of users, roles, and connected systems increases fast. Spreadsheets and email-based approvals quickly become unmanageable. This leads to longer review cycles and delayed decisions. As a result, critical access remains active far longer than it should.
This delay creates risk. The longer excessive or unnecessary permissions remain in place, the larger the attack surface becomes. In many cases, access that should have been revoked weeks earlier stays active simply because the process cannot keep up.
User access review automation changes this dynamic. By removing manual steps, an organization can:
Automation does more than just improve efficiency; it restores control. Instead of chasing completion metrics, teams can focus on verifying whether access is still justified. This is a crucial shift away from rubber stamp access certification and toward a process that actually reduces risk.
The scope of compliance is exploding. 91% of identity leaders have seen the scale of their reviews increase since 2022, and
99% of companies now conduct reviews primarily to satisfy regulatory frameworks.
However, when the focus is solely on satisfying auditors, the process becomes a "checkbox" exercise. This leads to the rubber stamp access certification phenomenon, where the goal is completion rather than security.
With 82% of leaders reporting that satisfying auditors requires high levels of effort, the exhaustion is palpable. Without applying clear access recertification best practices, organizations will continue to drown in paperwork while orphaned accounts and excessive entitlements – found in 98% of reviews – remain a wide-open door for attackers.
Even when organizations recognize the strategic importance of Identity and Access Management, a secondary hurdle often leads to a "white flag" mentality. The challenge lies in a specific hiring paradox that leaves even well-funded programs in a state of stagnation.
Building a modern, secure identity system requires the skills of an elite architect, someone capable of designing a "Formula 1" infrastructure. However, once that system is live, a disconnect appears.
High-level builders are rarely interested in the mundane, repetitive tasks of daily administration or troubleshooting MFA tickets. They are driven by high-stakes problem-solving, not the maintenance of a steady state.
This reality leaves leadership facing two equally risky scenarios:
1. The retention risk.
Paying a premium salary to an overqualified expert who, feeling underutilized by routine tasks, is likely already looking for the next challenge.
2.The capability gap.
Handing over a sophisticated, high-performance architecture to a generalist team that lacks the specialized knowledge to manage it.
This is the equivalent of handing a Formula 1 car to a driver who only knows how to navigate a standard sedan. The intentions are good, but the operational reality creates a dangerous vulnerability. When the team responsible for user access review automation or complex IAM workflows doesn't fully grasp the underlying architecture, the system slowly degrades.
Eventually, the lack of specialized oversight leads back to the very "theater" previously described, where the complexity of the tools overwhelms the staff, and access recertification best practices are abandoned in favor of whatever is easiest to manage.
The accumulation of these structural failures leads to consequences that are both technically dangerous and financially staggering. When access reviews are performed as theater, the "stage" isn't the only thing at risk – the entire organization becomes a target for exploitation.
The most immediate technical fallout is persistent privilege creep. Without a mature approach to access recertification best practices, users and former employees gradually accumulate permissions that far exceed their current roles.
Because reviewers often lack the necessary context regarding why access was originally granted or how it is being used, the default action is rarely revocation. This creates a massive, ever-growing attack surface.
Manual campaigns, which were intended to shrink this footprint, instead become the mechanism that allows orphaned or excessive permissions to linger indefinitely, directly violating the principle of least privilege.
The
Ponemon report highlights a sharp upward trend in the financial impact of identity-related vulnerabilities.
The total average annual cost of insider security incidents has reached US$19.5 million. This represents a $2 million increase compared to 2025.
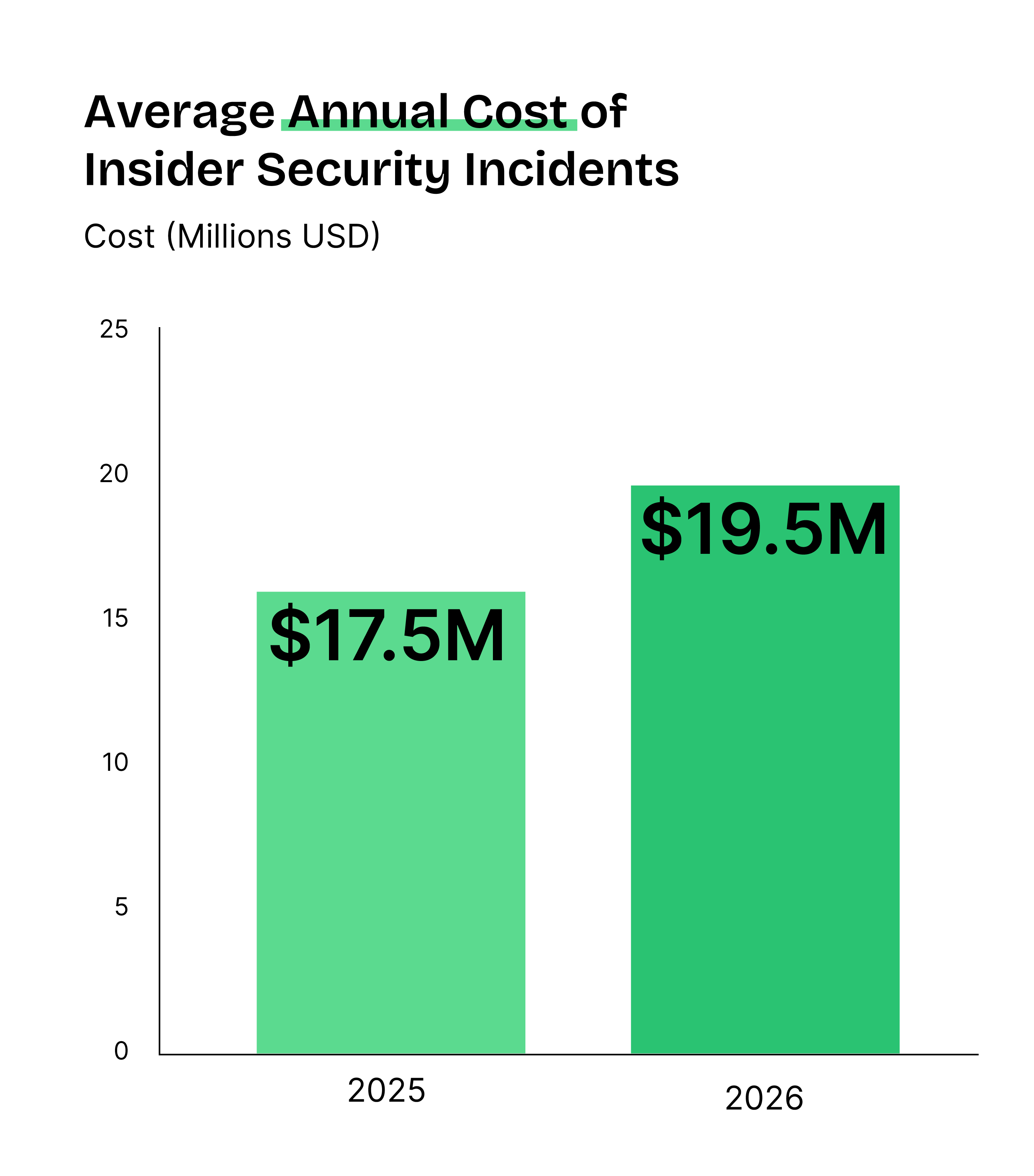
This financial drain isn't just the result of deliberate insider abuse. It is the price of an unmanaged environment where oversight is inconsistent and slow.
But what might be the biggest source of anxiety, in my opinion, is how long it takes to contain such issues – 67 days on average.
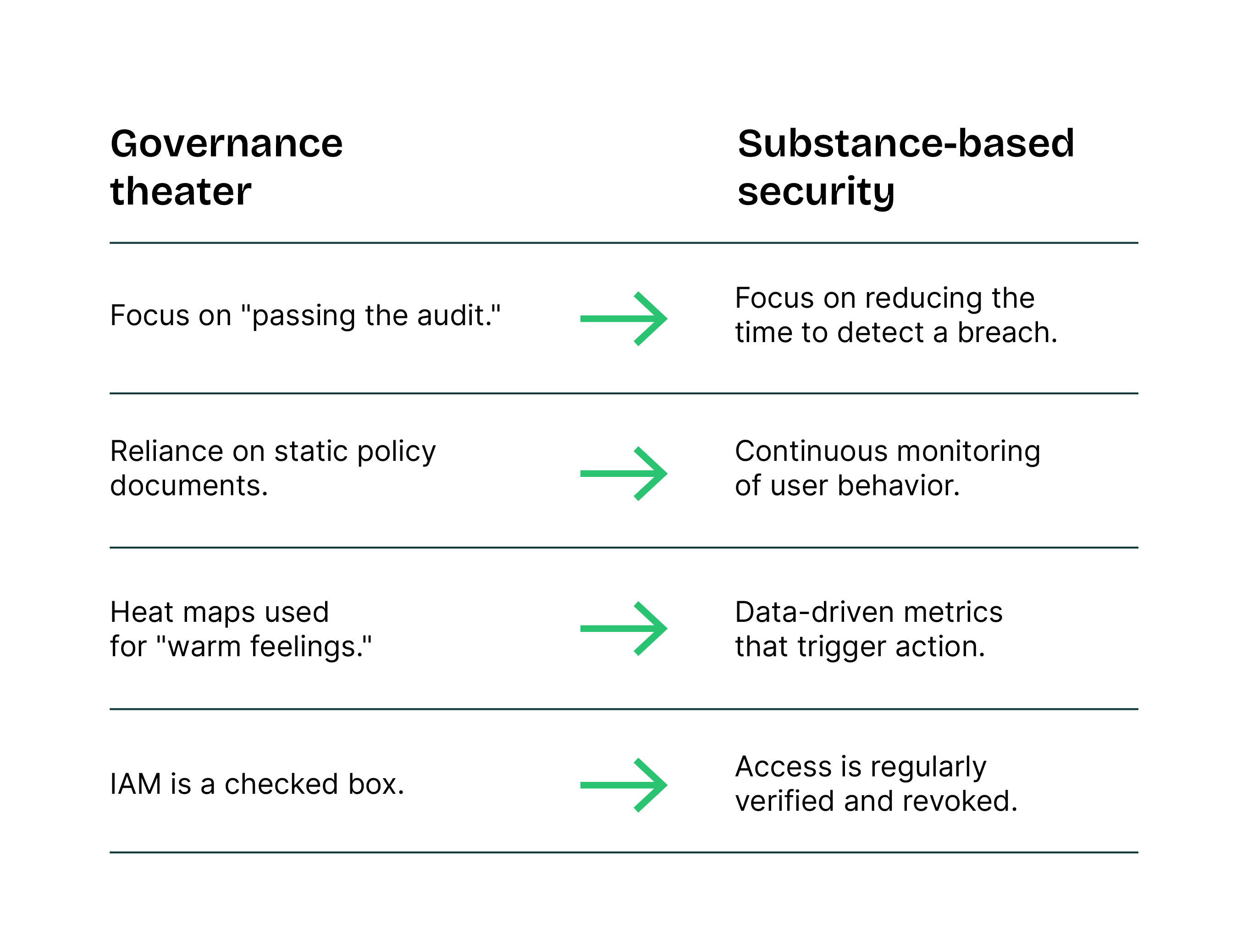
The core of the issue lies in the distinction between "compliance" and "actual security." While the artifacts of governance like signed policies provide a feeling of safety, they often fail to address the underlying risks.
I think that it’s more helpful to look at the habits that create a false sense of security than to study complex statistics.
Operational disruptions often hide behind the label of "technical glitches," but identity governance failures usually sit at the root. When organizations grant employees, developers, or contractors broad access rights such as full administrative control over cloud storage or production databases they eliminate the margin for error.
Neglecting access recertification best practices transforms a simple mistake into a catastrophe. Without a safety net, a single user with excessive privileges can trigger several high-stakes scenarios:
These actions rarely stem from malicious intent. Instead, human error finds a foothold in a lack of oversight. When managers treat reviews as a "rubber stamp" exercise, they fail to ask if a user truly needs the power to modify core resources.
A mature IAM program creates a buffer for the team. By tailoring access strictly to current requirements, an organization reduces the "blast radius" of a single accidental keystroke. Transitioning to user access review automation ensures that these guardrails remain in place, protecting the business from its own administrative debt.
Moving from "theater" to a functional security posture requires a shift in how the organization engages the reviewers themselves. I often see teams struggle because the process itself remains opaque and exhausting, not because they lack the will.
The most common enemy of a successful audit is "reviewer fatigue." When managers face a mountain of requests with no clear end in sight, the temptation to engage in rubber stamp access certification becomes overwhelming.
To fight this, I recommend moving away from the "one-size-fits-all" annual campaign.
Instead, a more effective strategy involves tiering the reviews based on risk. Organizations should run frequent, small-scale campaigns for privileged roles while reserving broader, lower-risk certifications for an annual or bi-annual cadence.
Breaking the work into manageable bites prevents the "check-the-box" mentality and keeps the focus where it matters most, which is on high-stakes access.
The "artifact trap" often stems from a lack of clarity. If a reviewer sees a role named APP_user_1232_new, they have no way of knowing what permissions that role actually grants. Without business-friendly descriptions and clear role naming conventions, the review process remains a guessing game.
I advocate for a "context-first" approach to form design. To make informed decisions, a reviewer needs more than just a cryptic ID; they need actionable data points integrated directly into the review interface.
Modern tools provide the necessary telemetry to turn a blind guess into an informed decision. For instance:
A bloated role catalog is often the silent killer of an effective IAM strategy. In my experience, organizations often mistake technical groups for business roles. I recently came across a situation where a client attempted to transform several hundred individual Workday groups into distinct roles. This level of granularity creates an unmanageable administrative nightmare, it doesn’t provide security.
To move away from this complexity, a strong Digital Advisor or IAM Program Manager must step in and enforce discipline. Successful programs rely on a rigorous role mining process to consolidate access into meaningful, logical clusters.
Often, the biggest hurdle is culture. Experts in the field must develop the ability to say "no" to requests for new roles driven solely by business convenience or "the way things have always been done."
By resisting the urge to over-complicate the system for the sake of comfort, organizations can implement access recertification best practices that actually scale. Refining the role structure is a prerequisite for successful user access review automation; without it, you are simply automating a mess.
Access reviews only reach their full potential when an organization integrates its applications directly with the governance platform. Without these connections, the "theater" continues. A reviewer might decide to revoke access, but someone (often a Service Desk agent) must then manually execute that change. This lag creates a dangerous window of risk.
Worse, a lack of integration leads to a visibility crisis. Permissions granted manually or "out-of-band" remain invisible to the IAM platform. If the system doesn't know an entitlement exists, it cannot include it in a review. To counter this, I recommend several high-impact access recertification best practices:
To wrap things up, we must realize that a stack of signed compliance reports does not equal a secure environment. If the process is a burden, managers will "rubber stamp" their way through it, and the organization will continue to carry the $1.9 million risk of an identity-based breach.
Security is a living process. The goal of an access review is to ensure that the right people have the right access for the right reasons – and not a single permission more.
Moving from "identity theater" to true governance requires a strategic partner who understands the balance between elite architecture and daily operational reality.
Whether you need to automate your review cycles, perform deep role mining, or integrate complex legacy systems, the experts at QWEY provide the specialized guidance to turn your IAM program into a proactive defense.
Reach out to us today to bridge the gap between compliance and actual security.